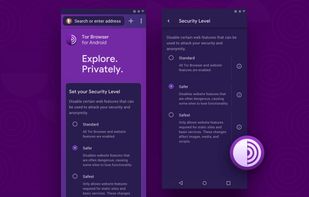
Enhance privacy with a secure, portable browser that hides your IP and encrypts connections on multiple platforms, maintaining anonymity.
Cost / License
- Free
- Open Source (MPL-2.0)
Application type
Platforms
- Mac
- Windows
- Linux
- Android
- Tor
- OpenBSD
- Flathub