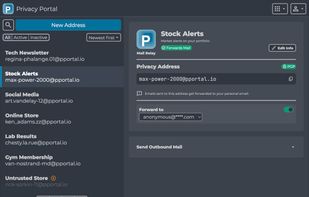
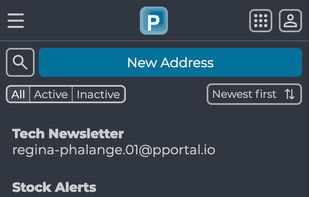
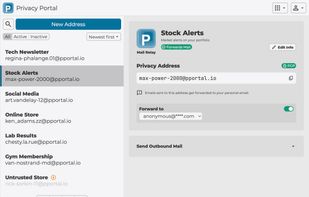
Mail Relay is Privacy Portal's email privacy service. It enables you to hide your personal email from third-parties, thus protecting your identity online and helping you reduce your digital footprint.
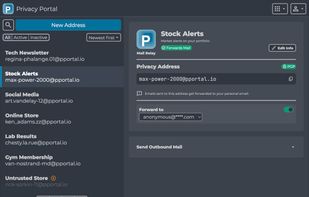
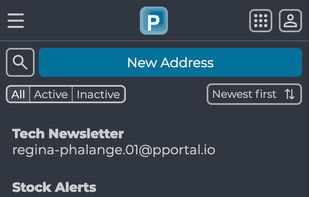

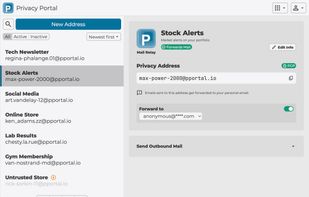
Mail Relay is Privacy Portal's email privacy service. It enables you to hide your personal email from third-parties, thus protecting your identity online and helping you reduce your digital footprint.

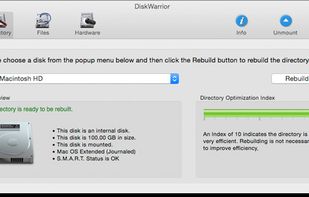
DiskWarrior is the safest, most technologically advanced, most powerful utility to eliminate directory damage and recover your files, folders and documents. DiskWarrior is so advanced it can even recover your data from a failing hard drive.
It gives its users the ability to create free, anonymous, encrypted temporary email accounts in a matter of seconds.
Ever lost your phone and you go to call it to listen for the ringer and remember its on silent mode? Now when you lost it you can text your phone and it will turn silent mode off, the ringer vol up, and start ringing.


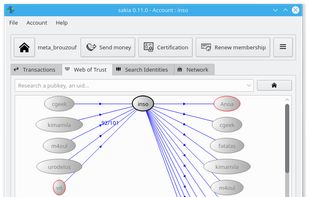
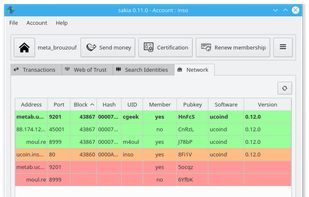
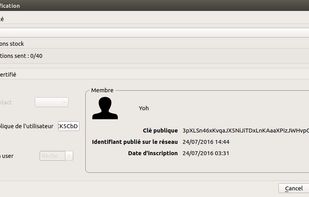
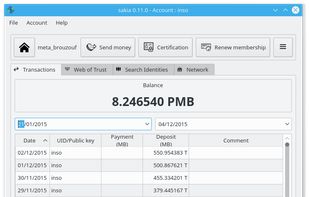
Explorer of DUniter communities network, to certify trusted peers, to generate an universal dividend, to send & receive transactions from anyone. Multi-currency-wallet for the currencies based on UCP - DUniter Protocol :
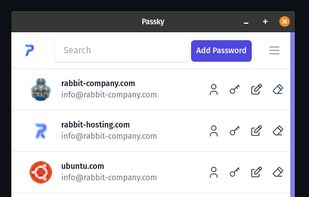
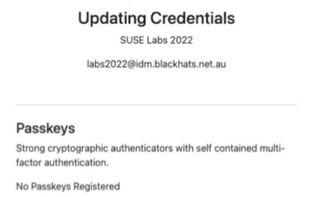
10Duke Identity Provider makes it easy for your customers to access and register to multiple applications with single username and password or using their favorite social login, secures profile data and easily integrates with leading business tools.




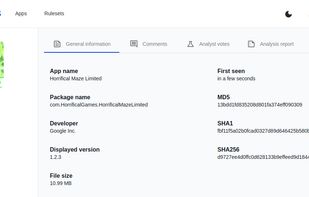
Koodous Query is a tool developed by Koodous, a platform specialized in the detection and analysis of malicious software. Its main function is to allow users to search for information on APK files through batches of hashes.



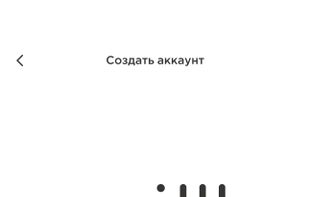
Shopot is a next-generation secure messenger designed for those who prioritize privacy, autonomy, and freedom from corporate or governmental surveillance. Unlike conventional messaging apps, Sh?pot operates entirely on proprietary infrastructure, with no reliance on third-party...


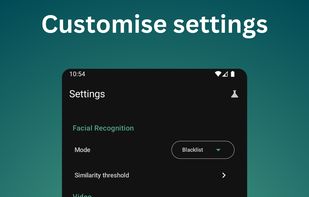
Sentinel Lens is a facial recognition surveillance app that sends Telegram alerts when unauthorized individuals are detected, based on a configurable blacklist and whitelist.




LibreCrypt (formerly DoxBox) is an open-source disk encryption for Windows and the successor of FreeOTFE

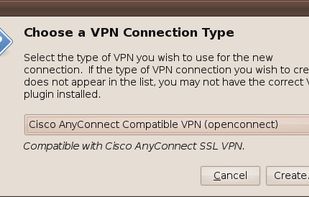
A VPN client compatible with Cisco AnyConnect VPN Client (now Cisco AnyConnect Secure Mobility Solution) and an open source substitute for Cisco's official Linux client.
A secure VPN app. This is a next-generation fast VPN with advanced privacy and security features. It offers you private internet access for online movies, TV shows, music, social networks etc.

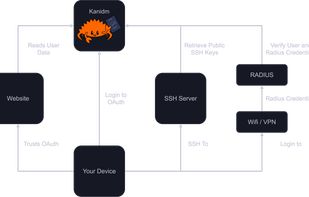
Kanidm is an identity management server, acting as an authority on account information, authentication and authorisation within a technical environment.
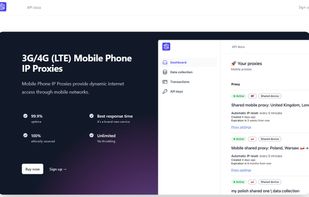
Easy integration and work with our cheap 4G mobile proxies via API. You can work with them through queries in json. There’s no need to import a proxy sheet, easy setup and operation. Easy to use in any proxy manager.
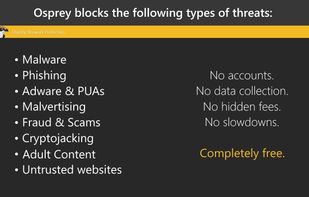
Karma Firewall app lets you take control back of your phone and block internet traffic to and from specific apps. This is a simple yet powerful firewall with an easy to use intuitive GUI which allows you to protect your sensitive data.

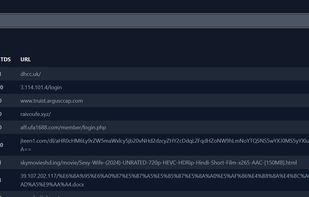
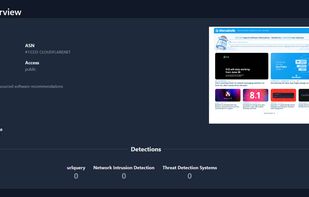
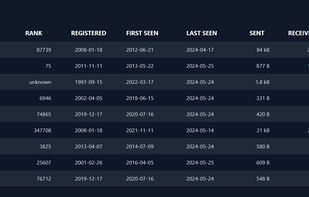
urlquery.net is like a lie detector test for the internet. We ask those sneaky URLs some tough questions and see if they're telling the truth or pulling a digital prank.

TrackerZapper is a Mac app that sits in your menubar and silently removes tracking parameters from any links you copy.
The Signal Protocol (formerly known as the TextSecure Protocol) is a non-federated cryptographic protocol that provides end-to-end encryption for voice and instant messaging conversations.
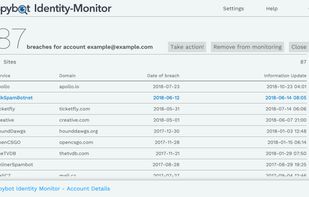
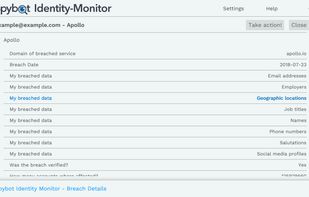
Get an overview where your account was leaked. Check if your information already is in the hand of hackers. It’s your data – your deserve to know!.

Should I Answer is free mobile security application protecting you against unsolicited, expensive, unwanted or unknown calls.