Tor is free software and an open network that helps you defend against traffic analysis, a form of network surveillance that threatens personal freedom and privacy, confidential business activities and relationships, and state security.
Phantom is described as 'The Phantom protocol is a system for decentralized anonymization of generic network traffic. It has been designed with the following main goals in mind:' and is a anonymizing network in the network & admin category. There are more than 10 alternatives to Phantom for a variety of platforms, including Linux, Mac, Windows, BSD and Android apps. The best Phantom alternative is Tor, which is both free and Open Source. Other great apps like Phantom are I2P, Hyphanet, Nym and i2pd (I2P Daemon).
Tor is free software and an open network that helps you defend against traffic analysis, a form of network surveillance that threatens personal freedom and privacy, confidential business activities and relationships, and state security.
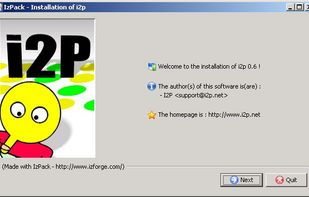
The I2P network provides strong privacy protections for communication over the Internet. Many activities that would risk your privacy on the public Internet can be conducted anonymously inside I2P.



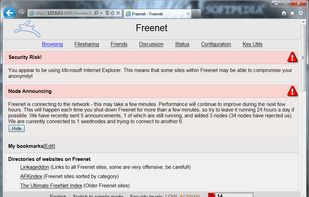
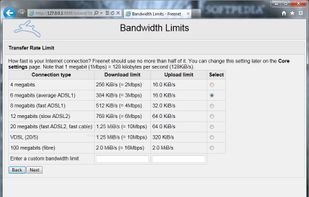
Hyphanet (former Freenet) is free software which lets you anonymously share files, browse and publish "freesites".

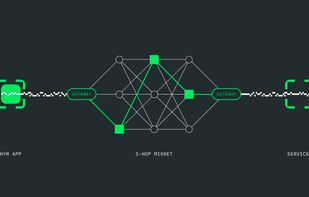
Protects internet traffic through a decentralized mixnet, hides metadata and communication patterns, enables anonymous transactions using re-randomizable credentials, and provides zero-knowledge proof access for privacy-focused messaging, blockchain, or application needs.

I2P (Invisible Internet Protocol) is a universal anonymous network layer. All communications over I2P are anonymous and end-to-end encrypted, participants don't reveal their real IP addresses.
A proof-of-concept scalable IPv6 meshnet, featuring end-to-end encryption, a unique spanning tree routing algorithm and aiming to implement novel backpressure routing metrics.

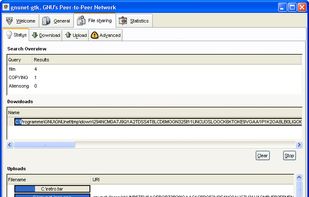
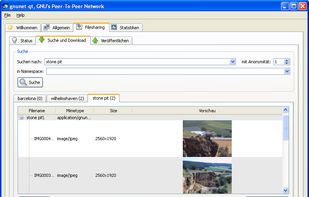
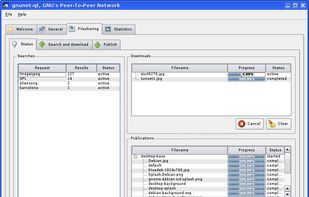
GNUnet is a framework for secure peer-to-peer networking that does not use any centralized or otherwise trusted services. A first service implemented on top of the networking layer allows anonymous censorship-resistant file-sharing.
The I2Pd Browser Bundle is a folder consisting of Purple I2P/I2Pd & Portable Firefox.
Bitmask is an open source application to provide easy and secure encrypted communication with a VPN. You can choose among different providers or start your own.


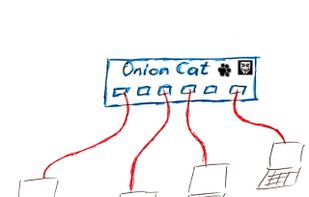
OnionCat creates a transparent IPv6 layer on top of TOR's hidden services. It allows users to anonymously access Internet services. It transmits any kind of IPv6-based data transparently through the TOR network on a location hidden basis.

LibreMesh is a set of modules extending the OpenWrt router distribution to create self-configuring wireless and wired mesh networks.