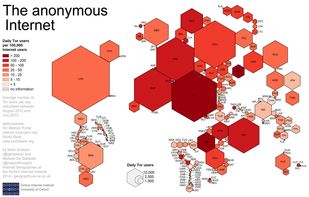
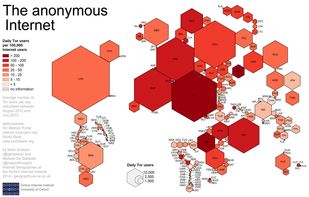
Tor is free software and an open network that helps you defend against traffic analysis, a form of network surveillance that threatens personal freedom and privacy, confidential business activities and relationships, and state security.
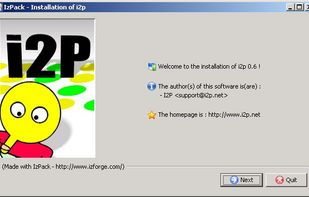
i2pd (I2P Daemon) is described as 'I2P (Invisible Internet Protocol) is a universal anonymous network layer. All communications over I2P are anonymous and end-to-end encrypted, participants don't reveal their real IP addresses' and is a anonymizing network in the security & privacy category. There are more than 50 alternatives to i2pd (I2P Daemon) for a variety of platforms, including Windows, Mac, Linux, Android and iPhone apps. The best i2pd (I2P Daemon) alternative is Tor, which is both free and Open Source. Other great apps like i2pd (I2P Daemon) are Matrix, Tor VPN, I2P and Hyphanet.
Tor is free software and an open network that helps you defend against traffic analysis, a form of network surveillance that threatens personal freedom and privacy, confidential business activities and relationships, and state security.
Open standard protocol enabling decentralized, encrypted instant messaging, VoIP signaling, IoT device connectivity, and persistent data management across federated servers without central control or single points of failure, bridging communication platforms.
A VPN that grants network-level privacy on mobile by routing app traffic through Tor, assigns each app a separate circuit for improved separation, bypasses app-level censorship, features per-app routing, security via Rust-based implementation, and awaits early adopter feedback.



The I2P network provides strong privacy protections for communication over the Internet. Many activities that would risk your privacy on the public Internet can be conducted anonymously inside I2P.



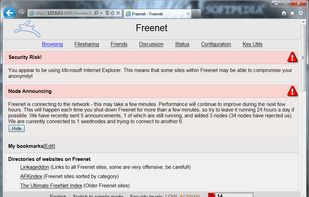
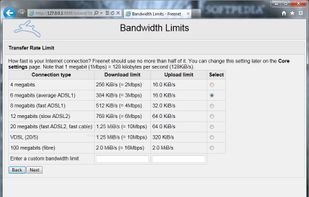
Hyphanet (former Freenet) is free software which lets you anonymously share files, browse and publish "freesites".

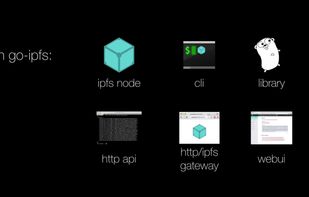
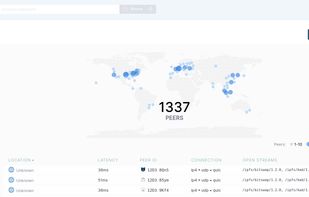
IPFS is a global, versioned, peer-to-peer filesystem. It combines ideas from Git, BitTorrent, Kademlia, SFS, and the web. It is like a single bittorrent swarm, exchanging git objects. IPFS provides an interface as simple as the HTTP web, but with permanence built in.


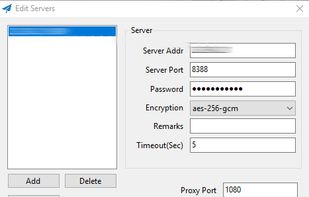
SOCKS5 proxy offering high-speed asynchronous networking, flexible encryption, and easy deployment. Optimized for cross-platform use on PC, Mac, mobile, and routers. Open-source design supports secure, uncensored, and private Internet access worldwide.
Journalists need safe access to information to research issues, communicate with sources, and report the news. Outline lets news organizations easily provide their network safer access to the open internet.


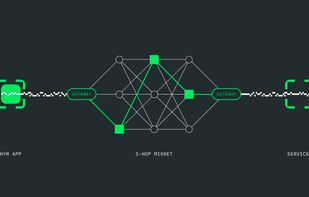
Protects internet traffic through a decentralized mixnet, hides metadata and communication patterns, enables anonymous transactions using re-randomizable credentials, and provides zero-knowledge proof access for privacy-focused messaging, blockchain, or application needs.

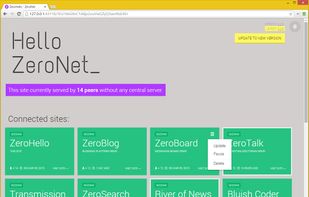
ZeroNet uses cryptography (Bitcoin library) and BitTorrent DHT (centralized trackers) to build a distributed censorship-resistant network.
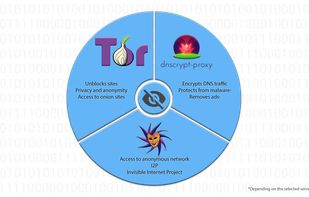
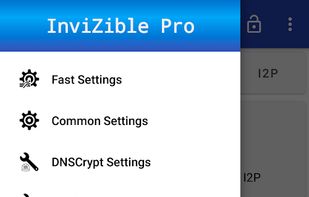
InviZible Pro uses DNSCrypt Protocol, Tor and i2pd (I2P Daemon) (PurpleI2P) to achieve maximum security, privacy and comfortable use of the Internet.


GNUnet is a framework for secure peer-to-peer networking that does not use any centralized or otherwise trusted services. A first service implemented on top of the networking layer allows anonymous censorship-resistant file-sharing.