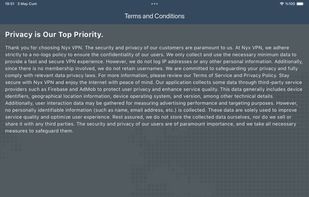
Completely free VPN app, which will ensure the security (confidentiality) of your personal data on the Internet.




i2pd (I2P Daemon) is described as 'I2P (Invisible Internet Protocol) is a universal anonymous network layer. All communications over I2P are anonymous and end-to-end encrypted, participants don't reveal their real IP addresses' and is a anonymizing network in the security & privacy category. There are more than 50 alternatives to i2pd (I2P Daemon) for a variety of platforms, including Windows, Mac, Linux, Android and iPhone apps. The best i2pd (I2P Daemon) alternative is Tor, which is both free and Open Source. Other great apps like i2pd (I2P Daemon) are Matrix, Tor VPN, I2P and Hyphanet.
Completely free VPN app, which will ensure the security (confidentiality) of your personal data on the Internet.







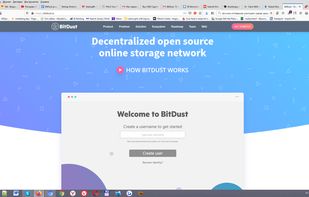
Imagine a decentralized network maintained by other users just like you. Here all your personal files are encrypted and only you hold the key to unlock them. Completely anonymous and secure.
Calypso, formerly Kommute, is a cross platfrom file sharing client using the anonymous network MUTE. Developped using C++ and Qt. For windows and linux, portable to other environments. You can try it by following the installation instructions below.


proXPN is the easiest way to secure your internet connection for free. Your privacy and security are protected with our military-grade VPN featuring 2048-bit encryption. proXPN works transparently to keep you protected at all times. Free beta accounts available now.

Decentralized VPN service providing privacy via blockchain, peer-to-peer architecture, and global exit nodes. Offers encrypted browsing, geo-unblocking, streaming, torrenting, multi-platform support, rewards for bandwidth sharing, and no registration required.



Freenet is a peer-to-peer platform for decentralized applications—communication, collaboration, and commerce without reliance on big tech. Your computer becomes part of a global network where apps are unstoppable, interoperable, and built on open protocols.



In early 2005, a few people fed up with the way the Internet was heading, began in earnest to create a large wide area network that was secure and lived in its own space. On this new network anyone would be free to do as they saw fit - roam about, host services, or just be...
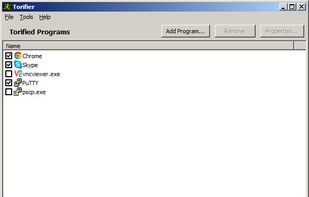
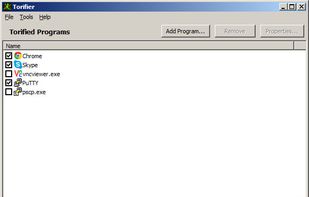
Torifier lets you tunnel software applications through Tor without the need to reconfigure them. An application is not required to have native proxy support in order to work with Torifier. Torifier is a Tor bundle, meaning the program will install the Tor software and will...
A post-Snowden VPN built on anonymity and security. Service requires you to think and have general understanding of software/networking setups. Intermediate level knowledge.
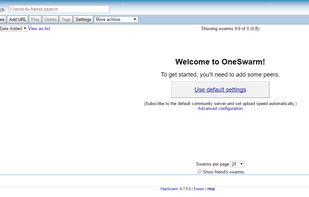
Supports both bittorrent protocol and a friend-to-friend version of the same protocol which in most situations makes you anonymous.