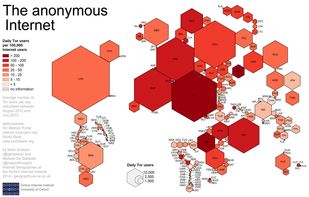
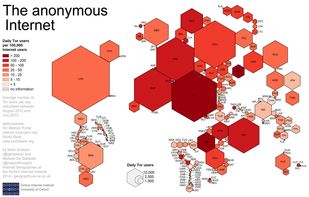
Tor is free software and an open network that helps you defend against traffic analysis, a form of network surveillance that threatens personal freedom and privacy, confidential business activities and relationships, and state security.
ninux is described as 'Ninux is an Italian wireless network community with the goal of creating and expanding a free, open and experimental computer network. It uses the OLSR (Optimized Link State Routing) Protocol, an IP routing protocol optimized for mobile ad hoc networks' and is an app in the security & privacy category. There are more than 10 alternatives to ninux for a variety of platforms, including Linux, Mac, Windows, BSD and Android apps. The best ninux alternative is Tor, which is both free and Open Source. Other great apps like ninux are I2P, Hyphanet, Nym and ZeroNet.
Tor is free software and an open network that helps you defend against traffic analysis, a form of network surveillance that threatens personal freedom and privacy, confidential business activities and relationships, and state security.
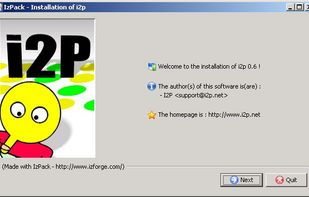
The I2P network provides strong privacy protections for communication over the Internet. Many activities that would risk your privacy on the public Internet can be conducted anonymously inside I2P.



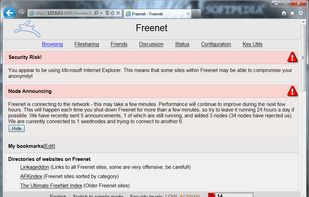
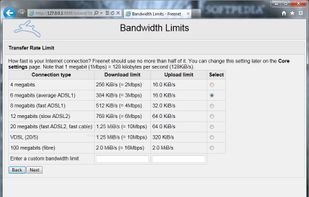
Hyphanet (former Freenet) is free software which lets you anonymously share files, browse and publish "freesites".

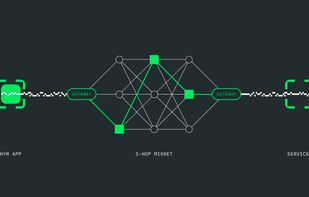
Protects internet traffic through a decentralized mixnet, hides metadata and communication patterns, enables anonymous transactions using re-randomizable credentials, and provides zero-knowledge proof access for privacy-focused messaging, blockchain, or application needs.

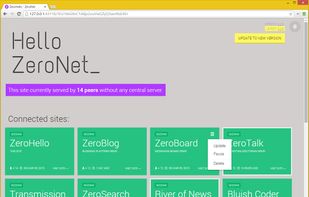
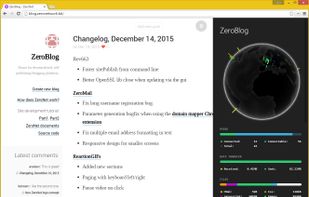
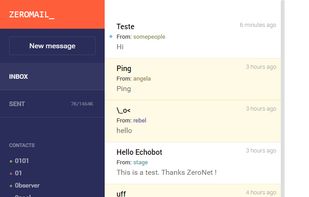
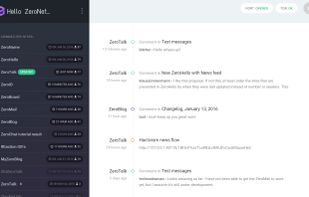
ZeroNet uses cryptography (Bitcoin library) and BitTorrent DHT (centralized trackers) to build a distributed censorship-resistant network.
I2P (Invisible Internet Protocol) is a universal anonymous network layer. All communications over I2P are anonymous and end-to-end encrypted, participants don't reveal their real IP addresses.
A proof-of-concept scalable IPv6 meshnet, featuring end-to-end encryption, a unique spanning tree routing algorithm and aiming to implement novel backpressure routing metrics.

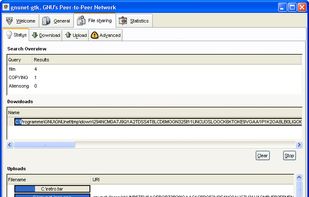
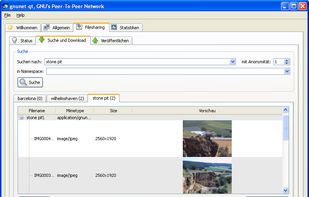
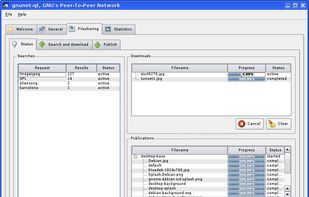
GNUnet is a framework for secure peer-to-peer networking that does not use any centralized or otherwise trusted services. A first service implemented on top of the networking layer allows anonymous censorship-resistant file-sharing.
The I2Pd Browser Bundle is a folder consisting of Purple I2P/I2Pd & Portable Firefox.
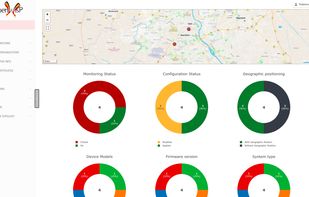
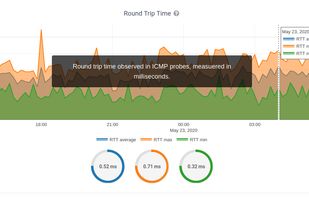
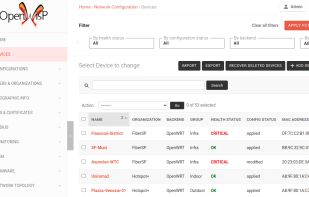
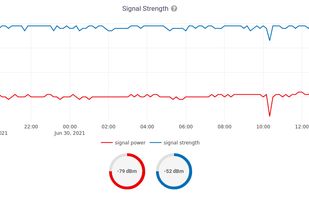
OpenWISP is a free and open-source platform for efficient IT network deployment, monitoring & management. It allows automation of many aspects of networks: from configuration to monitoring, RADIUS, hotspots, mesh and firmware upgrades, all backed by the reliability of the...