GladPass.com is a free web app that automatically creates unique, secure and random passwords based on Google's recommended combination of numbers, symbols and a mix of upper and lower case letters.
Cost / License
- Free
- Proprietary
Platforms
- Online
GladPass.com is a free web app that automatically creates unique, secure and random passwords based on Google's recommended combination of numbers, symbols and a mix of upper and lower case letters.
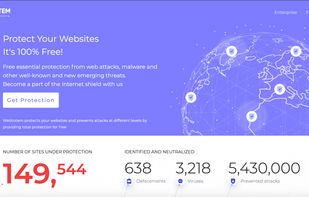
WebTotem is a SaaS which provides powerful tools for securing and monitoring your website in one place in easy and flexible way.
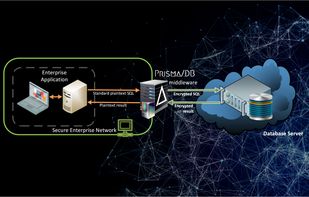
Aprismatic’s Prisma/DB is a secure data management and processing platform with a primary focus on data confidentiality. Exposing rich querying capabilities, precise encryption controls and high performance, it guarantees confidentiality of stored and processed data even if the...
Free continuous website security scanner and uptime monitor. Scan any site in 2 seconds, we checks TLS/SSL, security headers, DNS, exposed files, misconfigs and cookies.

CloudSploit provides continuous security monitoring, detailed reports, and risk detection for cloud infrastructure environments.

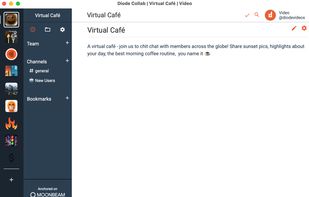
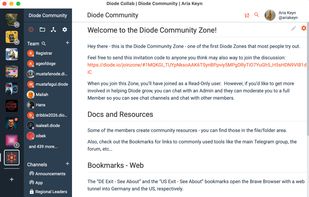
Diode Drive offering a secure alternative to Slack, Google Drive, Discord, and various messaging apps (Signal, Telegram, etc.) for those looking to regain ownership of their personal or work related data/information.

infosec-jobs.com aims to provide the most comprehensive job site related to all things Cyber Security. Our goal is to help hiring the best candidates and finding the most attractive positions in the InfoSec space.
75% of network intrusions in 2013 involved a weak, lost or stolen credential. TransAuth wants to make it easier to prevent the damage and cost associated with data breaches due to compromised passwords . Automatic Multifactor Authentication is faster, easier and more comprehens.

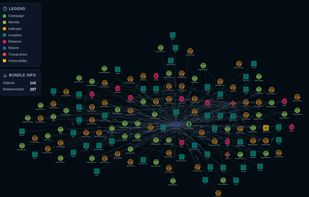
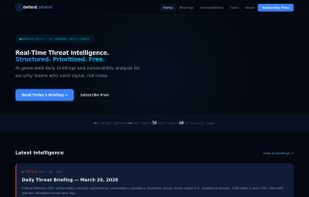
Threat Landscape is an automated threat intelligence platform built for security analysts and SOC teams who need high-confidence, actionable intelligence — without the manual triage.

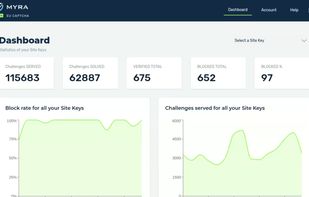
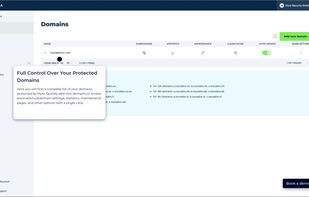
Myra Security is a cybersecurity provider specializing in protection for web applications and infrastructures. The company offers solutions such as DDoS protection, WAF, CDN, EU CAPTCHA, and Bot Management to help organizations ensure availability, performance, and compliance.





Business LOG is an advanced log management and SIEM platform designed to help organizations centralize, monitor, and retain logs for security, auditing, and regulatory compliance. It supports the collection, storage, correlation, and analysis of logs from multiple sources...

Hackerize is an essential security monitoring tool for websites, constantly protecting businesses from ever-evolving cyber threats.
Identify critical vulnerabilities at 10x speed without any configuration required with world's most intelligent web app & API security scanning platform, ZeroThreat.ai.




Free AI-powered cybersecurity intelligence platform delivering daily threat briefings, weekly vulnerability reports with remediation steps, and a curated directory of 59 security tools.
A zero-server, client-side PII sanitizer that redacts personal data from text before using AI tools like ChatGPT, working entirely offline.




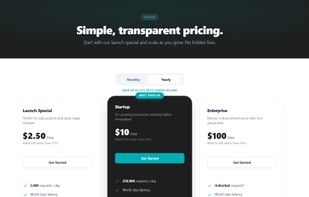
REST-based IP Geolocation & IP Intelligence API with IPv4/IPv6 support, ASN lookup, proxy detection, and bulk enrichment.

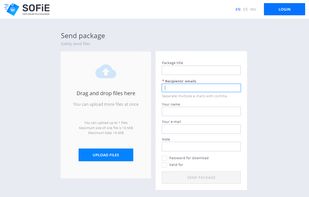
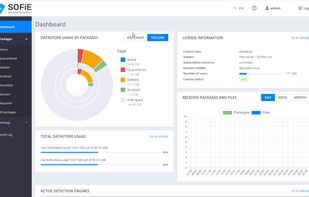
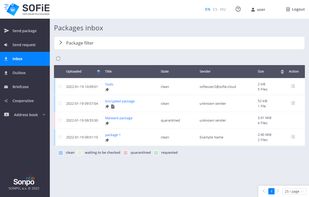
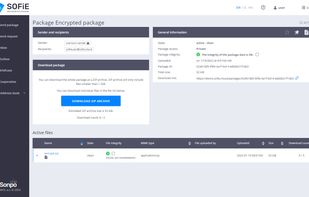
SOFiE is an application to exchange files of any size and type. Offer you a reliable solution with high security for receiving and sending files both inside a company and outside for communicating with other entities.
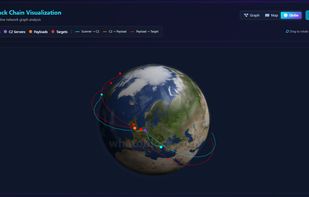
Whatoblock is a real-time cybersecurity threat intelligence platform with global botnet tracking, scanner detection, interactive threat search, and a live threat map.



Have you had enough of cookie banners? Forget about them! Ninja Cookie will take care of these and can say “no” to them for you!



Mails-Guard analyzes suspicious emails using AI to detect phishing attempts and malicious content, providing clear actionable recommendations without storing your data.

A free, cybersecurity-focused online tool that analyzes PCAP files and generates clear reports highlighting suspicious behaviors, security vulnerabilities, and other notable network events.

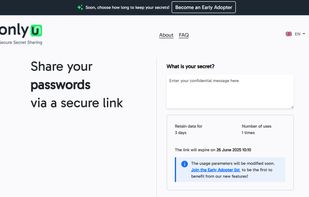
OnlyU is a free, secure platform for sending self-destructing messages and passwords. No signup is required, and all messages are end-to-end encrypted by default. Once read, messages are permanently deleted.
A principal função do Local Monitor é a identificação de intrusos em seu computador. Trojans Backdoors serão facilmente identificados, pois monitorando suas conexões você saberá exatamente o que está acontecendo em sua maquina...