X2y Av Ultimate
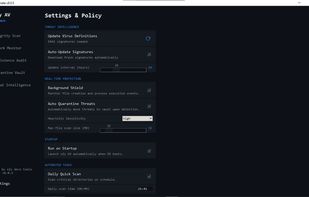
x2y AV Ultimate is a professional-grade security utility developed by x2y devs tools. It delivers genuine, non-AI, production-level system protection by utilizing a Hybrid Architecture to execute privileged system checks, real-time file monitoring, and advanced malware persistence analysis
Cost / License
- Free
- Open Source (MIT)
Platforms
- Windows
Features
Properties
- Privacy focused
- Lightweight
Features
- Works Offline
- No Tracking
- Malware Analysis
- No registration required
- Ad-free
- Dark Mode
X2y Av Ultimate News & Activities
Recent activities
 x2ydevstools added X2y Av Ultimate as alternative to COMODO Antivirus
x2ydevstools added X2y Av Ultimate as alternative to COMODO Antivirus x2ydevstools added X2y Av Ultimate as alternative to Sophos Home
x2ydevstools added X2y Av Ultimate as alternative to Sophos Home x2ydevstools added X2y Av Ultimate as alternative to F-Secure Anti-Virus
x2ydevstools added X2y Av Ultimate as alternative to F-Secure Anti-Virus x2ydevstools added X2y Av Ultimate as alternative to Emsisoft Anti-Malware
x2ydevstools added X2y Av Ultimate as alternative to Emsisoft Anti-Malware x2ydevstools added X2y Av Ultimate as alternative to AdwCleaner
x2ydevstools added X2y Av Ultimate as alternative to AdwCleaner x2ydevstools added X2y Av Ultimate as alternative to Trend Micro AntiVirus
x2ydevstools added X2y Av Ultimate as alternative to Trend Micro AntiVirus- x2ydevstools added X2y Av Ultimate as alternative to ClamAV and ZoneAlarm Antivirus
- x2ydevstools added X2y Av Ultimate as alternative to Avast One, Tron Script and McAfee Total Protection
 x2ydevstools added X2y Av Ultimate as alternative to Kaspersky Virus Removal Tool and Kaspersky AntiVirus
x2ydevstools added X2y Av Ultimate as alternative to Kaspersky Virus Removal Tool and Kaspersky AntiVirus x2ydevstools added X2y Av Ultimate as alternative to AVG AntiVirus, LoveLaceAV and ClamXav
x2ydevstools added X2y Av Ultimate as alternative to AVG AntiVirus, LoveLaceAV and ClamXav
X2y Av Ultimate information
What is X2y Av Ultimate?
x2y AV Ultimate
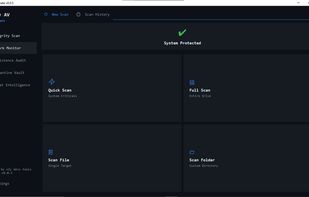
x2y AV Ultimate is a comprehensive endpoint security application for Windows delivering real-time malware protection, network traffic monitoring, system persistence auditing, and threat intelligence management from a single lightweight desktop application. Built for home users and security professionals alike, it operates entirely offline with no subscriptions, no cloud uploads, and no telemetry. Your files and scan results never leave your machine.
Multi-Layer Threat Detection
Every file is run through six independent detection layers in sequence. Hash Database Matching identifies known malware instantly by SHA256 and MD5 against a local SQLite database. ClamAV Engine Integration provides access to millions of signatures kept current via freshclam. YARA Rule Scanning executes rules fully compatible with the Yara-Rules community project. PE Binary Heuristics catches packed executables including UPX, MPRESS, and Themida without a signature. Behavioral Pattern Matching flags obfuscated PowerShell, process injection, and ransomware kill-chain commands. Entropy Analysis catches encrypted or packed payloads that evade every signature-based layer.
Real-Time Network Monitor
Every active TCP and UDP connection is mapped to its originating process and PID, with automatic flagging of C2 addresses, suspicious ports, and algorithmically generated domains. Right-click any connection to block it via Windows Firewall, terminate the process, capture a packet trace, or tag it with a MITRE ATT&CK technique.
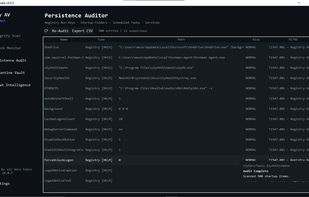
Persistence Auditor
Audits Registry Run keys, Startup folders, Scheduled Tasks, WMI commands, and Windows Services in one unified view with MITRE ATT&CK mapping. Right-click any entry to disable, delete, analyze, or export as a STIX 2.1 indicator for MISP or Splunk ingestion.
Quarantine Vault
Confirmed threats are moved to an isolated directory with no executable associations. Every file is tracked by original path, threat name, detection method, SHA256, and timestamp. Restore or permanently delete with a single click.
Threat Intelligence Center
Pull fresh indicators from MalwareBazaar, URLhaus, OpenPhish, and ClamAV on demand or on a daily automatic schedule. Look up any hash instantly against the local database.
Privacy
No data ever leaves your machine. No analytics, no crash reporting, no license calls. Everything is stored locally under your home directory.