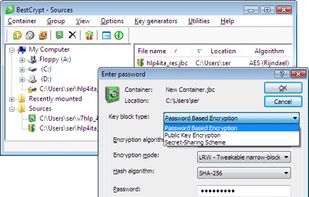
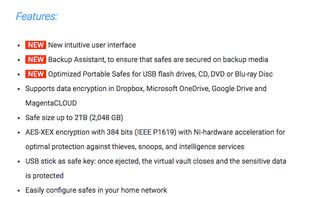
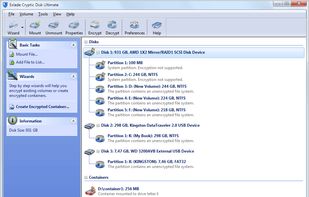
If your computer were ever to be stolen, are you certain that your personal information cannot be discovered? Jetico’s BestCrypt software automatically encrypts your files so that nobody can read the data unless they have the right password or keys.
Cost / License
- Paid
- Proprietary
Platforms
- Mac
- Windows
- Linux