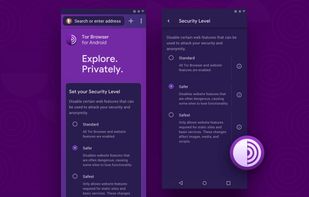
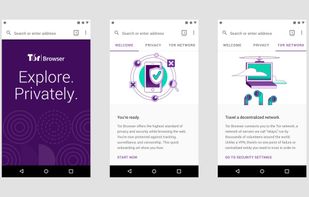
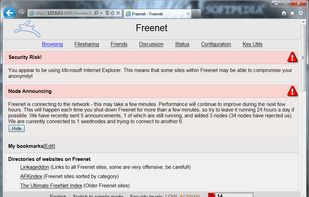
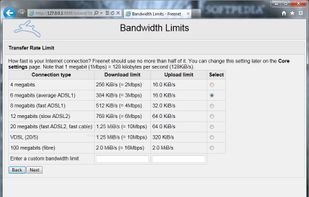
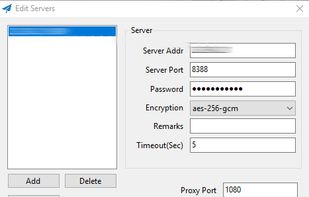
Experience true privacy online with a portable browser offering built-in proxy, encryption, and tracker blocking. Navigate without revealing location or browsing data, enjoying ad-free, secure surfing across platforms like Windows, Mac, Linux, and Android with no installation hassle.
Cost / License
- Free
- Open Source (MPL-2.0)
Application type
Platforms
- Mac
- Windows
- Linux
- Android
- Flathub
- OpenBSD