LessPass
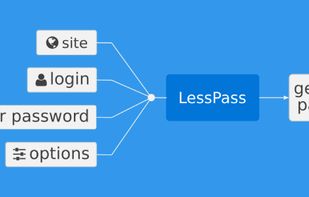
LessPass is an open source password manager. Instead of syncing a database of passwords, it generates them locally every time you put in a domain name, login and master password. There is no central database for hackers to break into.
Cost / License
- Free
- Open Source
Application type
Platforms
- Mac
- Windows
- Linux
- Online
- Android
- Self-Hosted
- Google Chrome
- Python
- Docker
- Mozilla Firefox
Features
Properties
- Lightweight
Features
- Password Generator
- Browser integration
- Browser-based
LessPass News & Activities
Recent News
Recent activities
- nazarzajya rated LessPass
- nazarzajya liked LessPass
- K0RR added LessPass as alternative to Locker Password Manager
 POX added LessPass as alternative to ExpressKeys
POX added LessPass as alternative to ExpressKeys Crypt0z0r added LessPass as alternative to Seed-Vault
Crypt0z0r added LessPass as alternative to Seed-Vault- az-doomer liked LessPass
- rated LessPass
LessPass information
Featured in Lists
## WHAT IS F-DROID ? F-Droid is an awesome app repository for FOSS (Free & Open Source Software) android apps. …
Using the **same password for several accounts** (messaging, social networks, online services, bank accounts...) can …
A list with 4 apps by A7lamLover without a description.
What is LessPass?
Stop wasting time synchronize your encrypted vault. Remember one master password to access your passwords, anywhere, anytime. No sync needed.
LessPass is a web application and works on all devices (computer, smartphone, tablet and your smartTV).
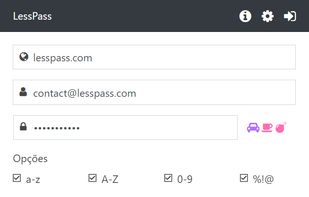
LessPass regenerates your passwords when you need them. No cloud storage is required. The way it works is that you enter a site, a login and a master password into the plugin and it uses this information to generate a unique password. Everytime you put that combination of site, login and password, it will generate the same password for the website.
We all know those sites that have special password rules. So you can't use the default options and have to remember the password is 6 characters long, only numbers. For this scenario we create what we call the "connected" version. Sign in, load or save complex password on LessPass Database.
You can also host your own LessPass Database through docker.






Comments and Reviews
LessPass is an open source browser plugin. It allows you to remember - or rather recall (important distinction) passwords for various websites. It works well but differently to most password managers, and the difference is worth understanding:
LESS PASS IS DIFFERENT TO MOST PASSWORD MANAGERS
Most password managers work by creating an encrypted database. A master password you choose is used to access the contents of the database. In the database you might store website logins and passwords, credit card details, notes, bookmarks, and whatever else you want/the password manager permits. That is how LastPass (don't confuse with Less Pass), 1Password, Dashlane, EnPass and KeePass all work (and relatives of KeePass like KeePassX, MacPass, KeeWeb and others). Either by design (e.g. LastPass, 1Password, Dashlane) or by choice (KeePass, EnPass you can sync the encrypted database between computers - either because the service offers it or because you can put your encrypted database into Dropbox or similar service.
The advantage of such a system is that quite a lot of information can travel with you between computers. You only need to download your database (again, either because a service like LastPass has a browser plugin that does that for you or because you access your sync folder and download it yourself) and then LOCALLY decrypt it to get at your information. Very convenient. It's what most people go for.
The weakness of that approach is that it creates a file that contains all your valuable data. Most password managers use the encryption standard AES-256, which is considered to be uncrackable, provided you chose a strong password. (Services like LastPass and apps like KeePass additionally put in bits of code that limit the number of guesses you can make at the password.) With all that, your database should be very secure. So even if someone were to hack LastPass servers (which has happened), or hack into your Dropbox account (which has also happened), your database should be nice and safe, even in the hacker's hands: they don't know the password and AES-256 is far too good for them to break in. Nevertheless, the weakness lies in the fact that all your data is in one place. That makes it an attractive place to TRY to hack/crack, for which reason LastPass, for example, have been targeted before. Now, many people find that to be an acceptable situation, which is fine.
Less Pass has a different design. It works by not having any database or file that could be stolen or decrypted. It works by using several things you input to calculate a unique password. So you open it, specify a domain name, e.g. "protonmail.com", a login e.g. "john.fastman" and a master password - a password you ALWAYS remember (the only one you need to). With this info, Less Pass uses a hash function to calculate a unique string of numbers, letters and symbols (you can set the length and complexity). Every time with these settings and with these inputs, it will generate the same password. The same math, with the same inputs always gives the same result, allowing you to recall the same password that you can then copy/paste into your login screen for whatever website you're visiting (protonmail.com in the example above). And that's it.
The advantages of this approach are:
you can go anywhere in the world, download it onto your computer, type in your details and have your password generated for you.
You never have to trust anyone to store your information securely, or that they have guarded a server correctly, or that they are implementing encryption correctly.
Commercial services like LastPass, 1password and Dashlane encrypt everything in your database, but NOT the URLs (web addresses) of your accounts. These are hashed (turned into a number) but in a way that's very easy to interpret. One of the problems with this is that these services, hackers and intelligence agencies can easily tell from looking at your database which websites you have accounts with. That could be used to identify you or profile you. KeePass (and its open source relatives - see above) don't do this despite having a centralized database. Less Pass also doesn't do this because it cannot - by design.
The disadvantages of this approach are:
unlike KeePass or LastPass, Less Pass isn't able to store notes, links, credit card details or anything else. It's just a password calculator.
It does not support 2-factor authentication, which means that all the security rests on the strength of your master password. In some situations, you could have a keylogger program on a computer (e.g. a compromised public computer) steal that password.
If you had to change your master password, it would innevitably mean that all your passwords, for all your websites, would have to change. That could be quite tedious to sort out.
If you need to change a password just for one website (e.g. your login for Diaspora), it becomes inconvenient to remember. Less Pass won't automatically remember that the old password is no longer good. You have to remember to increase a counter from '1' to '2' when generating the Diaspora password.
Password managers like KeePass and LastPass have either good browser integration or well-developed autofill capabilities. (KeePass uses the excellent KeeFox plugin for Firefox.) Less Pass has neither, which means that once your password is generated, you have to copy it to your clipboard and paste it into the login page's password field. That leaves your password in the clipboard, and a hacker will know to look there if your computer is compromised (or you're using compromised public computer).
OTHER PASSWORD MANAGERS WITH THE SAME SOLUTION:
Less Pass is not unique in its approach. Other password managers that use this design are Master Password and SuperGenPass. They vary by how well supported they are and whether they use a browser plugin, a website or a local client installed on the computer. Master Password is the closest thing to Less Pass - if Less Pass interests you, check out Master Password to see if that's even better for your needs.
IS LESS PASS GOOD/BETTER THAN THE ALTERNATIVES?
That's a personal choice based on your usage needs. I do not use Less Pass for the hundreds of domains I have accounts with. The main reason is the inconvenience associated with changing a password just for one account, and then remembering to have to increase the counter (see above). For that, the database-reliant method is better, and I would only trust open source apps, like KeePass (Windows & Linux), KeePassX (all platforms), MacPass (Mac), KeeWeb (all platforms) and their compatible relatives.
However, a good useage case for Less Pass is this: If you have collaborators you would wish to share passwords with, you can agree with them in person to use Less Pass, and what the master password should be. All you do then is email them what website/other input you wish to generate a password for and they can do the same thing on their computers using Less Pass as you can. In this way you can share passwords without really sending them insecurely, e.g. via email. For that, Less Pass is excellent.
Your text is excellent, I'll just add some information:
Another negative factor is that you need to remember what the password looks like. Some sites only support numbers and others do not accept special characters. All of this needs to be set in the password manually as well.
The question of "a public computer can see your password" I think it would only be possible to see the password entered. If you use a cell phone to use the master password and type what you see on it to the public PC you are committing only a single account and not the main one.
Can the issue of copying and someone spying on the clipboard be avoided by selecting the text and using drag and drop? I'm not sure, but I think so because he just copies without going through the transfer, right?
I really think that having 100 accounts on a system where updating item by item can take forever, but I believe its main use is much more for the security core. It does not serve well and I imagine that there are very few people who use it in all their accounts. I think people are much more likely to use only on 1, 2, or 8 accounts of their most sensitive piece of information. Like secret revenue from big companies, finance and that sort of thing. Then, I think it's wonderful how this program works.