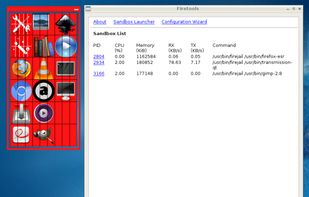
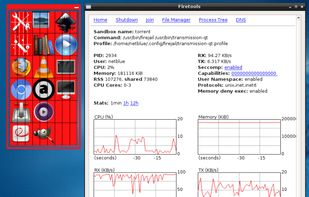
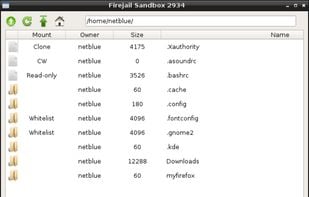
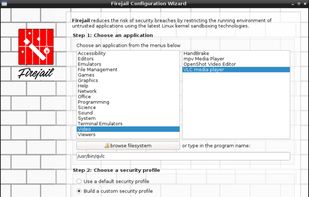
Firejail is a SUID security sandbox program that reduces the risk of security breaches by restricting the running environment of untrusted applications using Linux namespaces and seccomp-bpf.
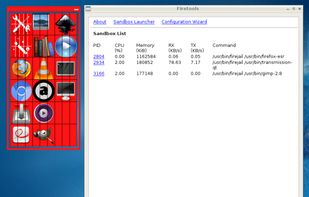
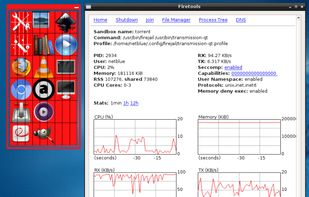
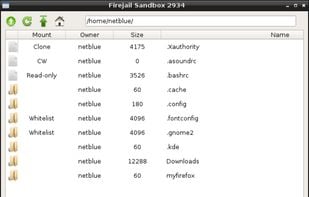
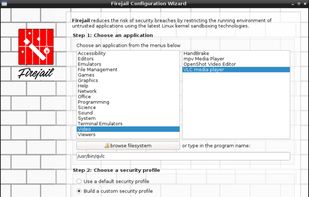
Firejail is a SUID security sandbox program that reduces the risk of security breaches by restricting the running environment of untrusted applications using Linux namespaces and seccomp-bpf.
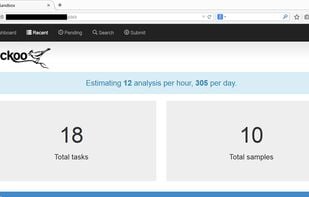
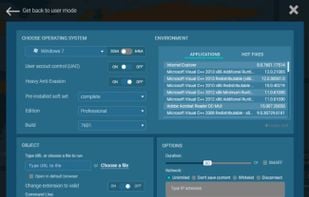
Cuckoo Sandbox is a modular, automated malware analysis system. Running from command-line on a Linux or Mac host, it uses python and virtualization (VirtualBox, QEMU-KVM, etc) to create an isolated Windows guest environment to safely and automatically run and analyze files to...


Rootkit Hunter is a POSIX system scanner for rootkits, backdoors and local exploits by running tests like:
Tiger is a Linux security tool that can be use both as a security audit and intrusion detection system.
Security auditing tool for systems running Linux, macOS, BSD, and other UNIX-based systems. It helps with compliance checking, finding vulnerabilities, and system hardening.

Fail2ban scans log files (e.g. /var/log/apache/error_log) and bans IPs that show the malicious signs -- too many password failures, seeking for exploits, etc. Generally Fail2Ban is then used to update firewall rules to reject the IP addresses for a specified amount of time...
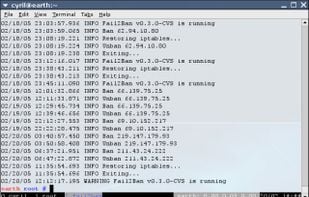
SSHGuard monitors services through their logging activity. It reacts to messages about dangerous activity by blocking the source address with the local firewall. SSHGuard employs a clever parser that can transparently recognize several logging formats at once (syslog, syslog-ng...
MailScanner is a open source email security system design for Linux-based email gateways. It is used at over 30,000 sites around the world, protecting top government departments, commercial corporations and educational institutions.
Valkyrie is a file verdict system that conducts several analysis using run-time behavior and hundreds of features from a file.

Joe Sandbox detects and analyzes potential malicious files and URLs on Windows, Android, Mac OS, Linux, and iOS for suspicious activities. It performs deep malware analysis and generates comprehensive and detailed analysis reports.
Hybrid-Analysis.com is a free malware analysis service powered by payload-security.com. Using this service you can submit files for in-depth behavior analysis.

ANY.RUN is interactive sandbox simplifies malware analysis of threats that target both Windows and Linux systems. ANY.RUN's threat intelligence products, TI Lookup, Yara Search and Feeds, help you find IOCs or files to learn more about the threats and respond to incidents faster.



REVERSS can analyze executables, URLs and PCAP files. It also show statistical data about found infections and the affected countries, etc. You can send the samples anonymously or logged in with Google to scan it privately.
As a malicious codes analysis service platform based on cloud and big data, malwares.com collects files to analyze automatically and to generate meaningful profiling information in order to provide cyber threats intelligence service.
AVCaesar is a malware analysis engine and repository, developed by malware.lu within the FP7 project CockpitCI.
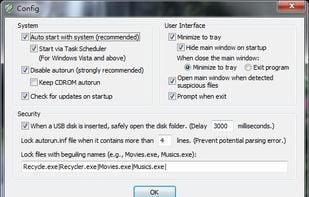
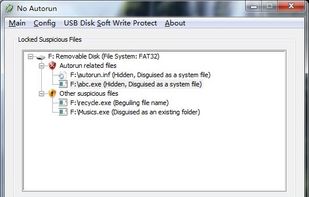
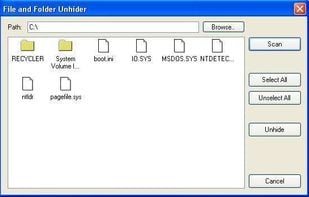
A tool to block viruses in USB flash/disk from auto-running. When a USB disk is inserted, this tool not only locks the "autorun.inf" file, but also locks all the autorun-related virus and other suspicious files.
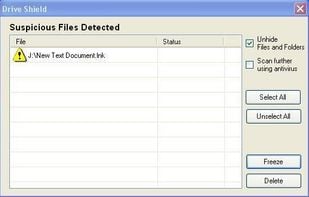
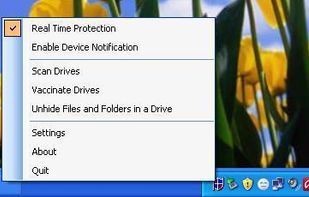
Protects PC against viruses from infected removable drives.
Shiela USB Shield (formely Shiela Rescue Shield) is a powerful first line defense against virus from infected removable drives. it locks autorun.inf and associate executable files in multiple instance, Delete/Freeze th.
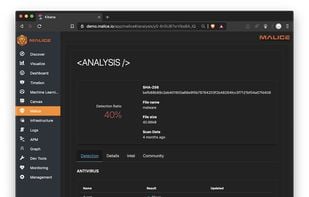
Malice's mission is to be a free open source version of VirusTotal that anyone can use at any scale from an independent researcher to a fortune 500 company.
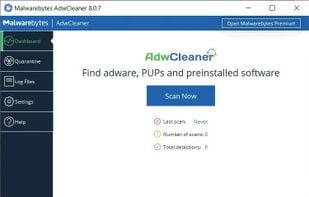
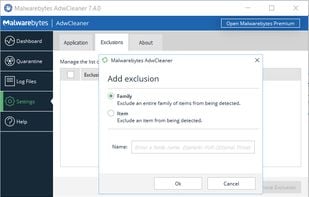
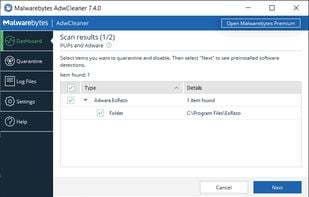
Removes adware, PUPs, toolbars, and browser hijackers with fast scans, no installation required, portable operation, and automated system cleaning.

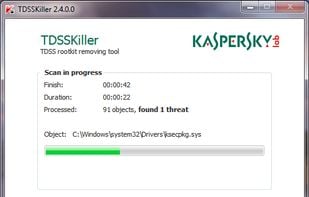
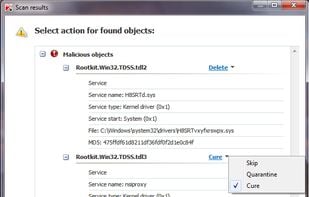
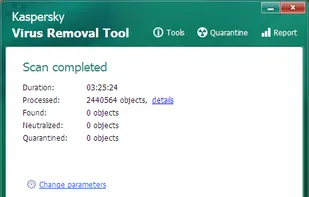
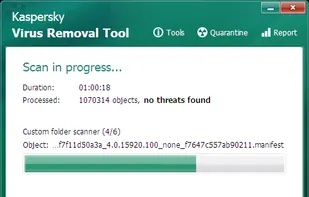
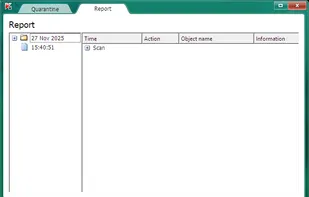
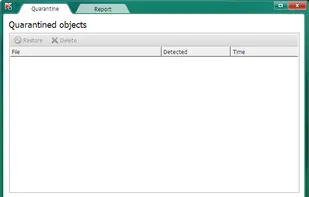
Kaspersky Virus Removal Tool is a free software intended to disinfect infected computers, removing viruses, Trojans, and spyware, as well as any other types of malware. Kaspersky Virus Removal Tool 2011 uses the same highly efficient algorithms for detecting malware as Kaspersky...
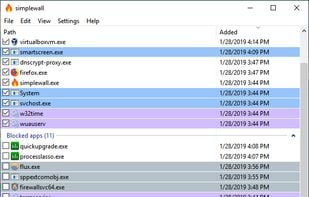
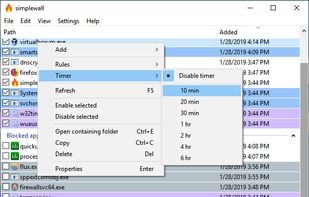
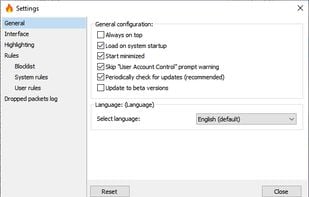
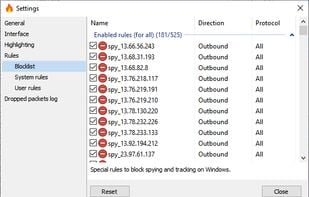
Simple tool to configure Windows Filtering Platform (WFP) which can configure network activity on your computer.
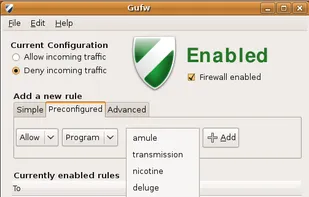
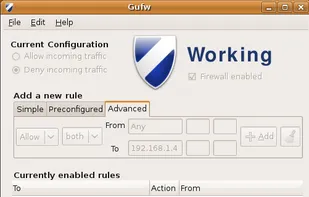
Gufw is an easy, intuitive way to manage your Linux firewall. It supports common tasks such as allowing or blocking pre-configured, common p2p, or individual ports port(s), and many others! Gufw is powered by Uncomplicated Firewall (ufw).

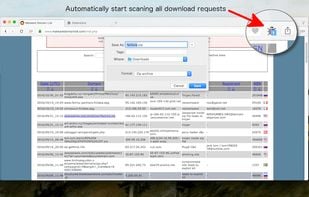
Download Virus Checker provides automatic check for all your downloads through 68 online anti-virus solutions. Basically the extension sends your download link to VirusTotal service and wait for its response.

Linux Malware Detect (LMD) is a malware scanner for Linux released under the GNU GPLv2 license, that is designed around the threats faced in shared hosted environments.
KicomAV is an open source (GPL v2) antivirus engine designed for detecting malware and disinfecting it. In fact, Since 1995, it has been written in C/C++ and it was integrated into the ViRobot engine of HAURI, 1998. I decided to re-create a new KicomAV.
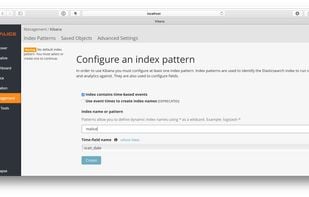
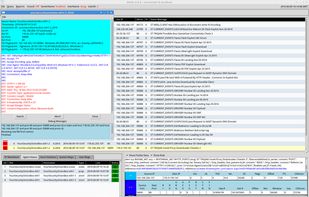
Security Onion is a free and open source Linux distribution for intrusion detection, enterprise security monitoring, and log management.


Open Source Tripwire software is a security and data integrity tool useful for monitoring and alerting on specific file change(s) on a range of systems.


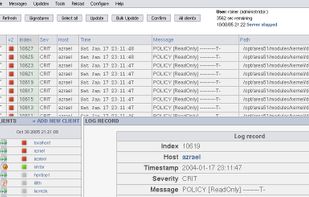
The Samhain host-based intrusion detection system (HIDS) provides file integrity checking and log file monitoring/analysis, as well as rootkit detection, port monitoring, detection of rogue SUID executables, and hidden processes.

Grsecurity® is an extensive security enhancement to the Linux kernel that defends against a wide range of security threats through intelligent access control, memory corruption-based exploit prevention, and a host of other system hardening that generally require no...


osquery is an operating system instrumentation framework for Windows, OS X (macOS), Linux, and FreeBSD. The tools make low-level operating system analytics and monitoring both performant and intuitive.
Maltrail is a malicious traffic detection system, utilizing publicly available (black)lists containing malicious and/or generally suspicious trails, along with static trails compiled from various AV reports and custom user defined lists, where trail can be anything from domain...


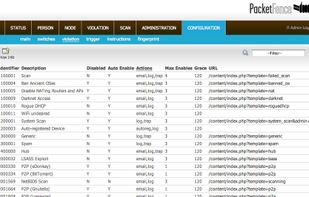
PacketFence is a Free and Open Source network access control (NAC) system. PacketFence is actively maintained and has been deployed in numerous large-scale institutions over the past years. It can be used to effectively secure networks - from small to very large heterogeneous...


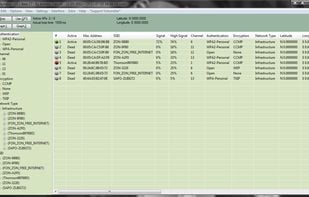
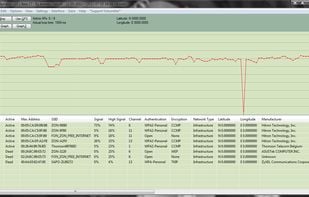
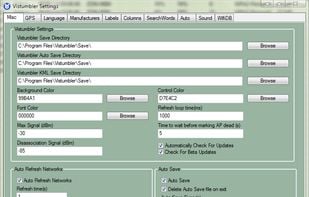
Vistumbler is a wireless network scanner and mapping utility designed for Windows Vista and above
amavisd-new is a high-performance interface between mailer (MTA) and content checkers: virus scanners, and/or SpamAssassin. It is written in Perl for maintainability, without paying a significant price for speed. It talks to MTA via (E)SMTP or LMTP, or by using helper programs.
Sysdig is open source, system-level exploration: capture system state and activity from a running Linux instance, then save, filter and analyze. Think of it as strace + tcpdump + lsof + awesome sauce.
SHADE Sandbox is an alternative for antivirus and a tool for virtualization. It locally virtualizes applications (i.e. internet browsers) and locks all incoming internet files and possible viruses in its safe virtual environment - a “sandbox”, keeping them isolated from the...

