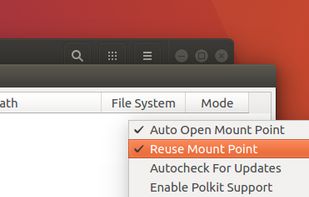
An open-source system tray utility for Windows, giving you quick access to your GnuPG keyring at any time with the ability to encrypt, decrypt and sign files on the fly.


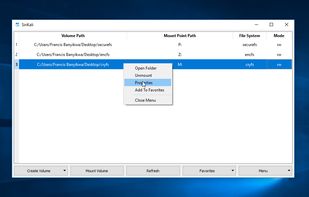
TrueCrypt is described as '[TrueCrypt is not exactly "Open Source", but the source is available. See the reviews to get more information.]' and is a leading Disk Encryption tool in the security & privacy category. There are more than 100 alternatives to TrueCrypt for a variety of platforms, including Windows, Linux, Mac, Android and iPhone apps. The best TrueCrypt alternative is VeraCrypt, which is both free and Open Source. Other great apps like TrueCrypt are Cryptomator, Picocrypt, LUKS and File Lock PEA.
An open-source system tray utility for Windows, giving you quick access to your GnuPG keyring at any time with the ability to encrypt, decrypt and sign files on the fly.


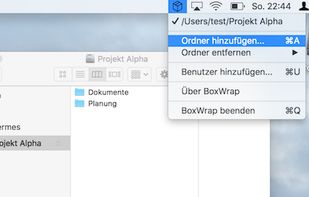
Encrypts and protects your files on your machine, before they hit your disk and the cloud: Collaborate with others, end to end encrypted.
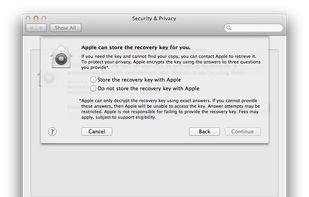
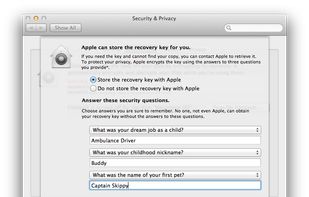
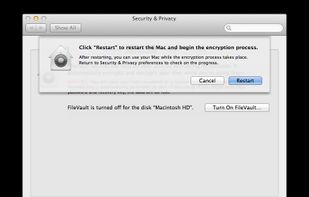
FileVault full-disk encryption uses XTS-AES-128 encryption with a 256-bit key to help prevent unauthorized access to the information on your startup disk.

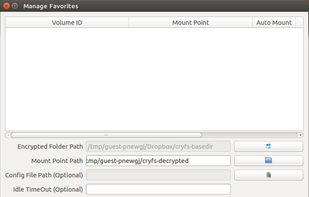
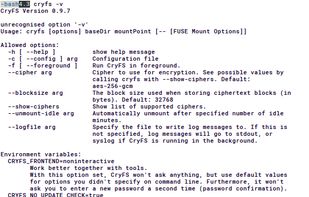
CryFS encrypts your files, so you can safely store them anywhere. It works well together with cloud services like Dropbox, iCloud, OneDrive and others.
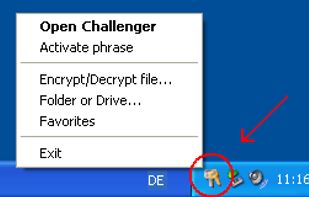
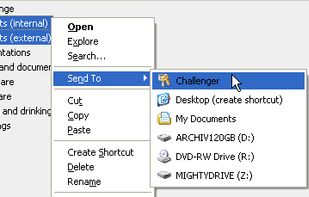
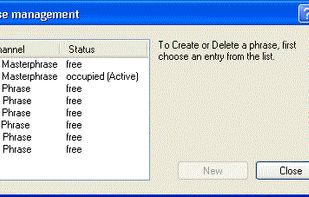
Challenger is a software for the encoding of files, folders and drives. For the installation and for the execution simple user rights suffice. Thereby the program is mobil usable on an USB flash drive too.

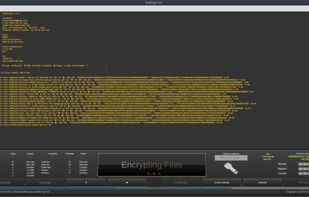
FinalCrypt uses the most unbreakable encryption: "One Time Pad" Encryption and has a well designed graphical user interface and an equally advanced command line interface for large automations.

AreaGuardNeo is file encryption and USB protection tool integrated with Microsoft Active Directory.




Password protection and strong encryption of the external and internal drives, flash drives, backup drives, etc.


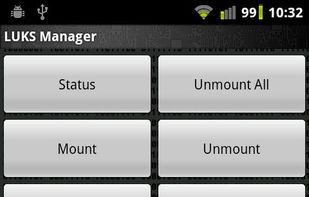
LUKS Manager provides on-the-fly encryption (AES by default) to virtual folders on Android devices.


ZONECENTRAL offers companies high levels of security by encrypting files so that their access is exclusively reserved to authorized and identified users. Free of any organizational constraints, ZONECENTRAL is simple to deploy.