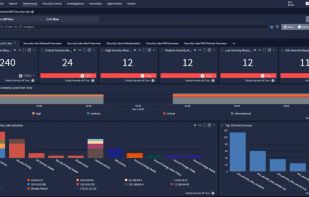
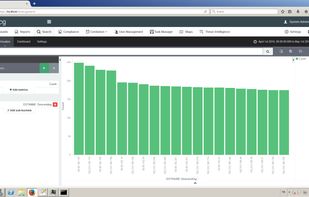
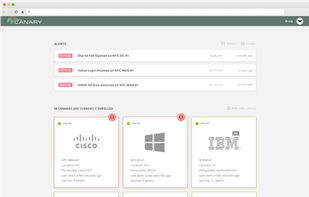
Graylog is a powerful Security Information and Event Management (SIEM) solution offering a robust log analytics platform that simplifies the collection, search, analysis, and alerting of all types of machine-generated data.
Cost / License
- Freemium
- Proprietary
Application type
Platforms
- Self-Hosted
- Online
- Software as a Service (SaaS)