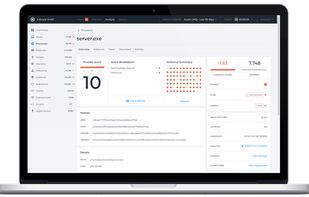
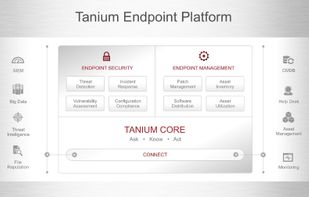
Cloud-based endpoint platform for real-time detection, prevention, and response to threats using lightweight sensors, advanced machine learning, graph analysis, and threat intelligence—instantly identifying known and unknown attacks for seamless enterprise protection.