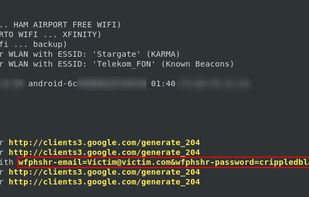
Standalone man-in-the-middle attack framework used for phishing login credentials along with session cookies, allowing for the bypass of 2-factor authentication.
Cost / License
- Free
- Open Source (BSD-3-Clause)
Platforms
- Mac
- Windows
- Linux
- BSD

Standalone man-in-the-middle attack framework used for phishing login credentials along with session cookies, allowing for the bypass of 2-factor authentication.

Pirates, Vikings and Knights II pits three teams against each other in a struggle for wealth, power and total domination. The game features many different game modes including Territory, where players fight to control key locations in the map; Holy Grail, where players seek to...



One of the best ways to compromise a computer is with physical access. Many of us have likely left our laptops unattended (perhaps in a hotel room while traveling?). It'd be nice to know if somebody attempted to hack it! ya?
Dead creatures roam the streets, the whole world has fallen into darkness and fear. Be ready to take a part in brutal battle! Are you tired from zombies fight games and zombies shooting games.

Get ready for an airheaded scary games, enter into the world of horror games! In this grammys house game, step into the realm of Halloween Horror Night, where the bravest bighead souls and even the most airheaded of thrill-seekers gather to face scary monster fears.




Prepare to be immersed in the terrifying world of horror gaming, where advancements in 3D graphics and offline gameplay have elevated the fear factor. Leading the pack of survival horror games is SCP Pipe Head, a game that has redefined the genre with its bone-chilling intensity.




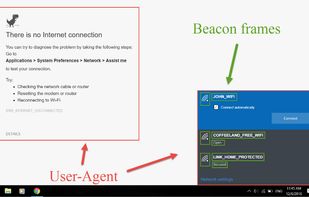
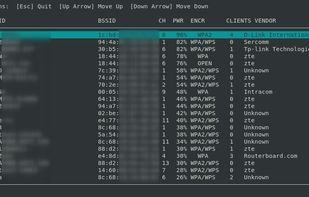
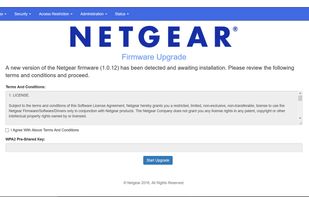
Wifiphisher, penetration testers can easily achieve a man-in-the-middle position against wireless clients by performing targeted Wi-Fi association attacks. Wifiphisher can be further used to mount victim-customized web phishing attacks against the connected clients in order to...