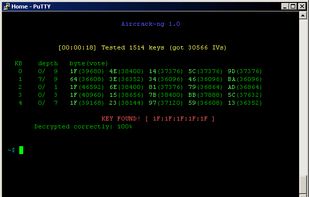
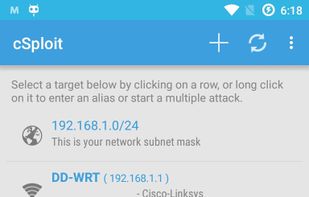
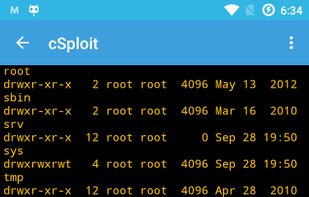
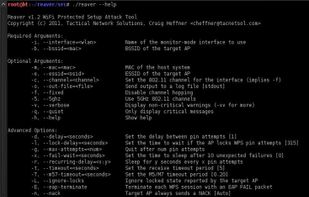
Wifite is described as 'Automated wireless attack tool. Wifite was designed for use with pentesting distributions of Linux, such as Kali Linux, Pentoo, BackBox; any Linux distributions with wireless drivers patched for injection. The current version 2 complete re-write of the original' and is a penetration testing tool in the security & privacy category. There are six alternatives to Wifite for Linux, Android, Windows and Android Tablet. The best Wifite alternative is Aircrack-ng, which is both free and Open Source. Other great apps like Wifite are Fern Wifi Cracker, cSploit, reaver and Waircut.