A proof-of-concept scalable IPv6 meshnet, featuring end-to-end encryption, a unique spanning tree routing algorithm and aiming to implement novel backpressure routing metrics.
Cost / License
- Free
- Open Source
Platforms
- Mac
- Windows
- Linux
- Android
- BSD

LEAP Encryption Access Project is described as 'LEAP is a non-profit dedicated to giving all internet users access to secure communication. Our focus is on adapting encryption technology to make it easy to use and widely available' and is a VPN service in the security & privacy category. There are seven alternatives to LEAP Encryption Access Project for a variety of platforms, including Android, Windows, Mac, Linux and F-Droid apps. The best LEAP Encryption Access Project alternative is Yggdrasil, which is both free and Open Source. Other great apps like LEAP Encryption Access Project are i2pd (I2P Daemon), Bitmask, Torifier and Tachyon VPN.
A proof-of-concept scalable IPv6 meshnet, featuring end-to-end encryption, a unique spanning tree routing algorithm and aiming to implement novel backpressure routing metrics.

I2P (Invisible Internet Protocol) is a universal anonymous network layer. All communications over I2P are anonymous and end-to-end encrypted, participants don't reveal their real IP addresses.
Bitmask is an open source application to provide easy and secure encrypted communication with a VPN. You can choose among different providers or start your own.


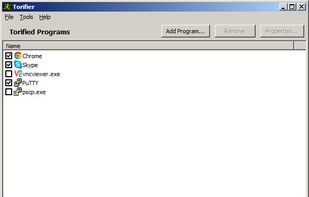
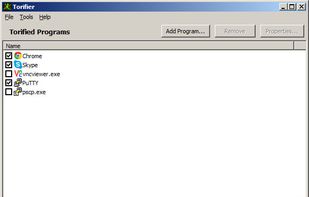
Torifier lets you tunnel software applications through Tor without the need to reconfigure them. An application is not required to have native proxy support in order to work with Torifier. Torifier is a Tor bundle, meaning the program will install the Tor software and will...



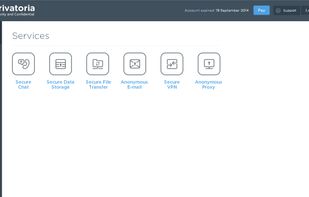
Privatoria.net is a service which provides secure communication, anonymous surf and secure file sharing for individuals and business. All security services are united together in Privatoria. It includes Secure VPN and anonymous proxy, that enable surf anonymously, change IP...



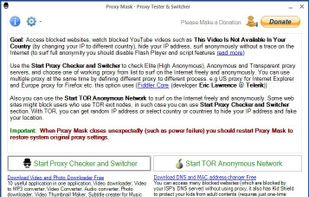
Main Features: All in one application: TOR, VPN and Proxy; Hide your IP address; Bypass Internet censorship and filtering; Hide your online activities from your ISP; Access blocked websites; Access Geo-restricted web contents (e.g.