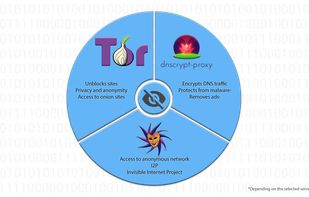
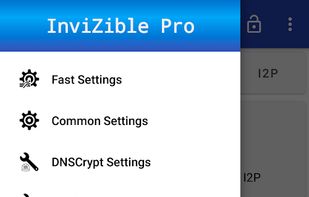
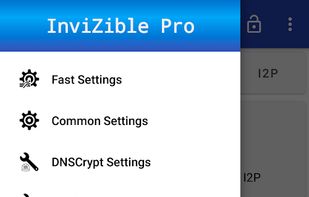
InviZible Pro uses DNSCrypt Protocol, Tor and i2pd (I2P Daemon) (PurpleI2P) to achieve maximum security, privacy and comfortable use of the Internet.

+5

InviZible Pro uses DNSCrypt Protocol, Tor and i2pd (I2P Daemon) (PurpleI2P) to achieve maximum security, privacy and comfortable use of the Internet.


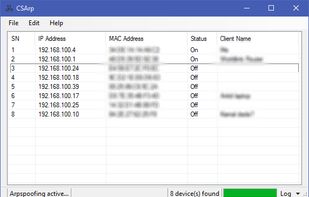
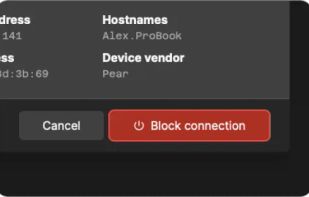
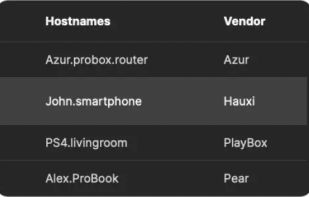
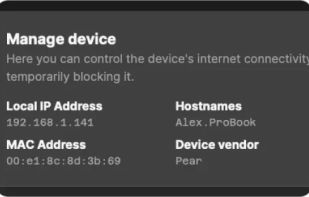
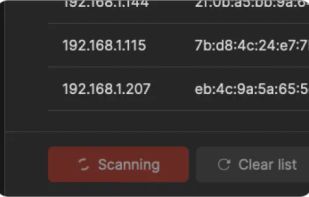
An arpspoofing program that lets users launch spoofed arp requests to disrupt connections in a LAN.