PE-sieve scans a given process, searching for the modules containing in-memory code modifications. When found, it dumps the modified PE. Detects inline hooks, hollowed processes, Process Doppelgänging etc. Can be used for unpacking malware.
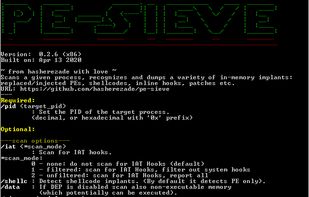
PE-sieve scans a given process, searching for the modules containing in-memory code modifications. When found, it dumps the modified PE. Detects inline hooks, hollowed processes, Process Doppelgänging etc. Can be used for unpacking malware.
Deviare In-Process is a code interception engine for Microsoft Windows®. It is a dual license library, GPLv3 and Commercial. The source code is available at GitHub.
Deviare is a powerful Code Interception Library, with a very simple interface that lets you hook many processes on your own application without any IPC coding. It can be used in any COM supporting languages as C++, VB and .NET.
Microsoft Research Detours v3 Professional is a library for instrumenting arbitrary Win32 functions on x86, x64, and IA64 machines. Now you can intercept Win32 functions by re-writing the in-memory code for target functions.
"madCodeHook" offers everything you need to hook code (mostly APIs). Supports Delphi 4-7, Delphi 2005-10.1 Berlin (32bit and 64bit), Borland C++ Builder 5-6, Borland C++ Builder 2006-10.1 Berlin (32bit only for now), MSVC++ (32bit and 64bit).

HookBytes is a powerful, self-hosted webhook management platform that serves as an open-source alternative to Hookdeck. Built with Laravel, it provides enterprise-grade webhook processing, monitoring, and debugging capabilities without vendor lock-in.
