SYRN
SYRN is a threat intelligence platform that helps cybersecurity teams monitor vulnerabilities and manage their attack surface.
Cost / License
- Freemium (Subscription)
- Proprietary
Platforms
- Online
Features
- Vulnerability management
SYRN News & Activities
Recent activities
- skidrow88 liked SYRN
- skidrow88 added SYRN
- POX updated SYRN
 skidrow88 added SYRN as alternative to Vulners API, Vulnerability Management Platform and Vulmon Alerts
skidrow88 added SYRN as alternative to Vulners API, Vulnerability Management Platform and Vulmon Alerts
SYRN information
What is SYRN?
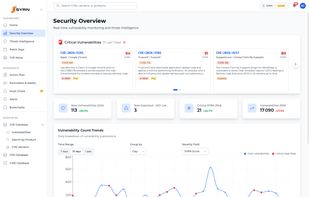
SYRN is a continuous threat intelligence and vulnerability management platform designed to assist cybersecurity teams in monitoring threats, mapping attack surfaces, and prioritizing remediation. The platform correlates published vulnerabilities with an organization’s actual technology stack and converts voluminous vulnerability data into targeted alerts and prioritized remediation plans tailored to specific environments. It addresses the challenge of managing thousands of vulnerability reports by transforming noise into actionable intelligence.
The platform follows a four-step workflow. The process begins with perimeter configuration through definition of networks, domains, cloud environments, or application stacks. SYRN then automatically discovers and catalogs technologies in the environment, including frameworks, libraries, services, and versions, with technology templates available for common stacks. Continuous correlation between the technology inventory and threat intelligence feeds, including vulnerability databases and community sources, yields actionable remediation recommendations ranked by the SYRN Score.
The SYRN Score extends standard vulnerability ratings by factoring exploit availability, probability estimates, threat intelligence signals, and asset-specific context. The platform aggregates threat data from more than fifteen sources such as national vulnerability databases, early warning lists, certified exploit repositories, and community feeds. Advanced filtering options allow selection of threats based on severity, exploit status, source, or publication date. Twenty four hour monitoring across the full infrastructure triggers immediate alerts when threats impact defined assets.
Asset management capabilities create a unified inventory that tracks digital assets, technologies, versions, and dependencies across all perimeters. Configurable alert rules notify security teams when new vulnerabilities align with predefined criteria. Automated remediation plans deliver clear action steps with expected impact to streamline correction workflows. REST API access supports integration with existing security operations and automation pipelines. The platform operates without requiring agent installation and minimal configuration enables monitoring to begin within minutes.