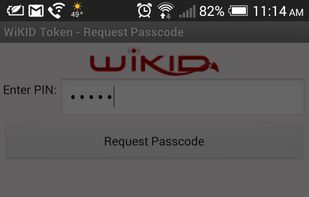
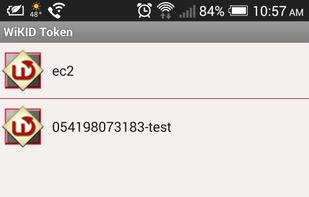
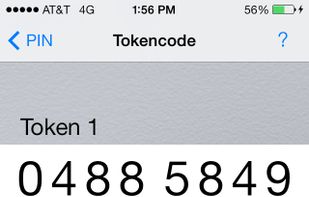
The WiKID Strong Authentication System is a highly scalable, secure, self-hosted two-factor authentication system. It is simple to implement and maintain, allows users to be validated automatically, requires no hardware tokens, has a simple API for application support (via Ruby...
Cost / License
- Paid
- Proprietary
Platforms
- Mac
- Windows
- Linux
- Windows Mobile
- Android
- iPhone
- Blackberry
- Chrome OS