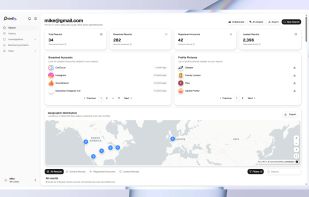
Mozilla Monitor arms you with tools to keep your personal information safe. Find out what hackers already know about you and learn how to stay a step ahead of them.

Have I Been Pwned is described as 'Website repository that checks what sites your email address was used on were compromised' and is a very popular Data Breach tool in the security & privacy category. There are more than 25 alternatives to Have I Been Pwned, not only websites but also apps for a variety of platforms, including Windows, SaaS, Mac and Linux apps. The best Have I Been Pwned alternative is Mozilla Monitor, which is both free and Open Source. Other great sites and apps similar to Have I Been Pwned are Data Breach Observatory, Intelligence X, DeHashed and LeakCheck.io.
Mozilla Monitor arms you with tools to keep your personal information safe. Find out what hackers already know about you and learn how to stay a step ahead of them.

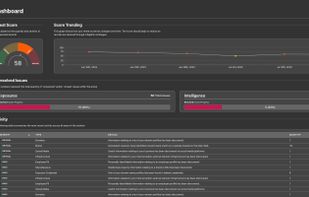
Automated system scans dark web sources to deliver real-time breach alerts when sensitive data or credentials are discovered, empowering businesses to investigate, respond promptly, prevent further exposure, and maintain security by identifying compromised accounts and files.

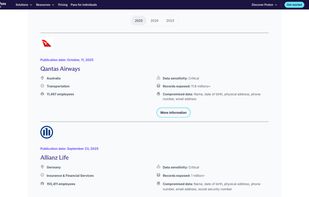
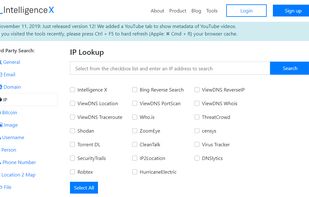
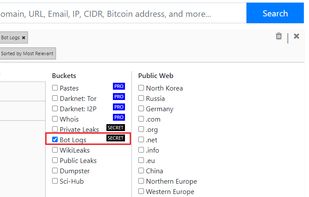
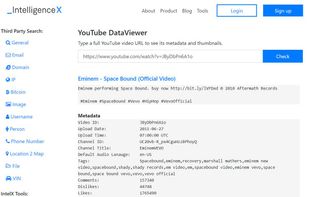
Intelligence X is a search engine and data archive. Search Tor, I2P, data leaks and the public web by email, domain, IP, CIDR, Bitcoin address and more.
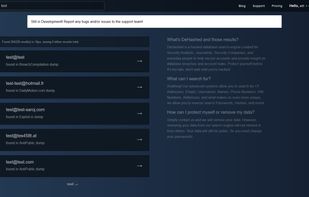
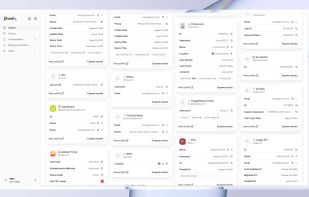
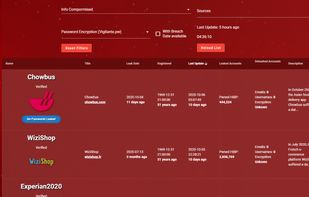
DeHashed is the largest & fastest data breach search engine. You can search for IP address, email, username, name, phone, VIN, address, and more! We have true wild card, dork usage, and we offer a real search engine experience! It's also free!.
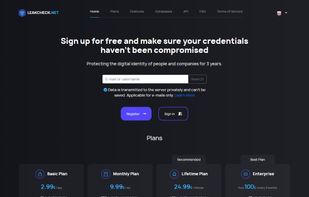
LeakCheck offers a search engine with a database of more than 7 billion leaked records. Users can search for leaked information using email addresses, usernames, phone numbers, keywords, and domain names. Our goal is to safeguard the data of people and companies.

Identity Guard is a service that specializes in identity theft and credit protection, aiming to protect individuals and families from fraud. It has served over 38 million people and boasts high Trustpilot ratings.

The industry leading database lookup. We pride ourselves in being faster than all of our competitors, wile maintaining a very large selection of private databases.



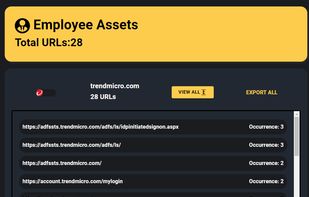
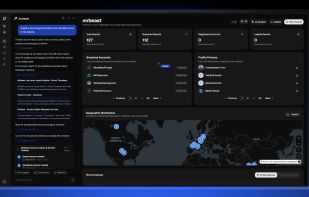
With expertise developed at the cybercrime intelligence division at the prestigious 8200 cyber unit at the IDF, Hudson Rock’s powerful cybercrime threat intelligence feed provides invaluable data for infrastructure protection, end-user protection, and supply chain risk...



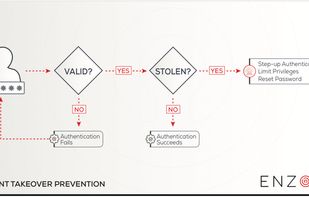
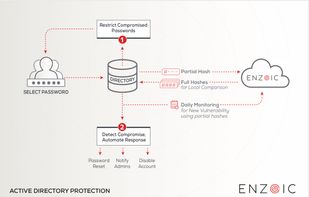
Enzoic provides solutions to detect compromised credentials and prevent attackers from unauthorized access accounts. With an Active Directory plugin and APIs, your organization is protected without any unnecessary friction to the user experience.
Osintly is rebuilt from the ground up with collaboration and AI at its core. New: shared workspaces, team management, and AI that summarizes results, detects patterns, and generates reports automatically.
Protect your account, discover its leaks, avoid using insecure passwords. Breach search engine powered by LeakCheck.net. Check if your password was compromise before it's too late. More results than HIBP.

DarkInvader is an external attack surface intelligence platform, that collect threat intelligence across the dark and surface web, helping to identify threat vectors that exist across in your attack surface.
If you have a Firefox Account you can add multiple emails in Firefox Monitor and look across all breaches.