Agent Vault
An open-source credential broker by Infisical that sits between your agents and the APIs they call.
Cost / License
- Free
- Open Source
Platforms
- Mac
- Linux
- Docker
Agent Vault
Features
Properties
- Privacy focused
Features
- Ad-free
- No Tracking
- No registration required
- Dark Mode
- Works Offline
- AI-Powered
Agent Vault information
What is Agent Vault?
An open-source credential broker by Infisical that sits between your agents and the APIs they call. Agents should not possess credentials. Agent Vault eliminates credential exfiltration risk with brokered access.
Why Agent Vault?
Traditional secrets management relies on returning credentials directly to the caller. This breaks down with AI agents, which are non-deterministic systems vulnerable to prompt injection that can be fooled into leaking its secrets.
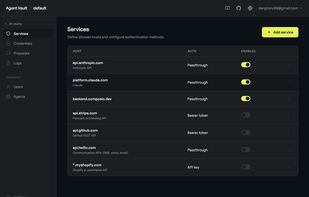
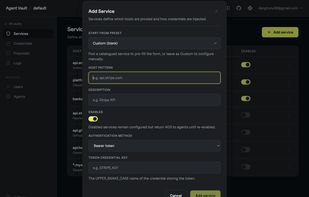
Agent Vault takes a different approach: Agent Vault never reveals vault-stored credentials to agents. Instead, agents route HTTP requests through a local proxy that injects the right credentials at the network layer.
- Brokered access, not retrieval - Your agent gets a scoped session and a local HTTPS_PROXY. It calls target APIs normally, and Agent Vault injects the right credential at the network layer. Credentials are never returned to the agent.
- Works with any agent - Custom Python/TypeScript agents, sandboxed processes, and coding agents like Claude Code, Cursor, and Codex. Anything that speaks HTTP.
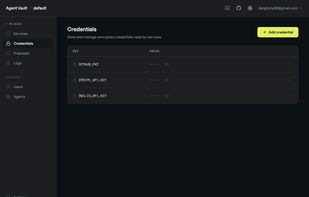
- Encrypted at rest - Credentials are encrypted with AES-256-GCM using a random data encryption key (DEK). An optional master password wraps the DEK via Argon2id, so rotating the password does not re-encrypt credentials. A passwordless mode is available for PaaS deploys.
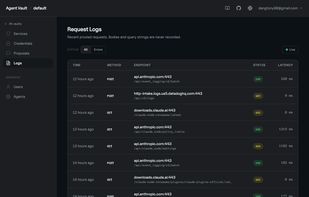
- Request logs - Every proxied request is persisted per vault with method, host, path, status, latency, and the credential key names involved. Bodies, headers, and query strings are not recorded. Retention is configurable per vault.