iOS SQLite vulnerability found via Contacts app
A new security vulnerability in Apple's flagship mobile operating system has been discovered and demonstrated, and it involves manipulating the OS's built-in Contacts app. This vulnerability impacts an estimated 1.4 billion devices running versions of iOS all the way from iOS 8 up to the latest betas of iOS 13.
As showcased by Check Point security at this year's Def Con conference, the exploit has been known for over four years, with Apple believing that it could only be exploited by an unknown and unisigned application, which is a non-issue for any iOS device that hasn't been jailbroken. At this year's Def Con, however, Check Point was able to show how the built-in Contacts app can be modified on any unlocked iPhone, iPad, and iPod touch running up to one of the latest betas of iOS 13.
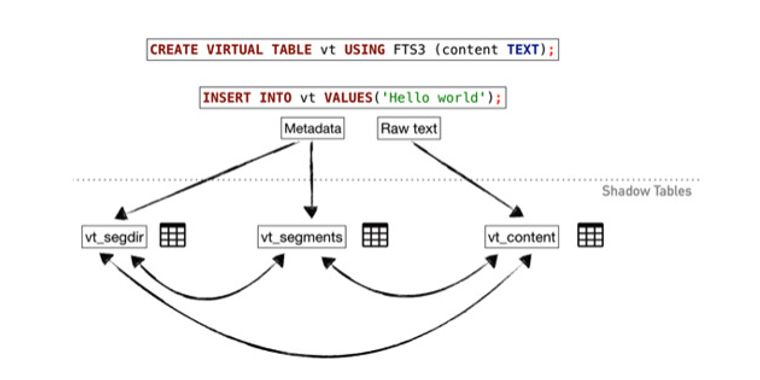
The exploit utilizes SQLite's unsigned databases and this slightly modified Contacts app in order to show how it could be used to run malicious code. The demonstration only showed an app crash, but could be used to, for example, steal passwords.
The report that Check Point released concerning the exploit stated the following:
"We established that simply querying a database may not be as safe as you expect. We proved that memory corruption issues in SQLite can now be reliably exploited."
Check Point has sent both its research and methodology to Apple in order to assist the company in patching the exploit for future versions of iOS. In the meantime, make sure you keep an eye on your iOS devices so that no one has access to them while they are unlocked and you're uncertain what they are doing on it.
Further coverage: AppleInsider Forbes
