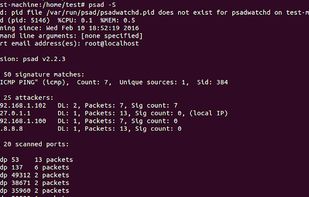
Cowrie is a medium interaction SSH and Telnet honeypot designed to log brute force attacks and the shell interaction performed by the attacker. Cowrie also functions as an SSH and telnet proxy to observe attacker behavior to another system.
Cost / License
- Free
- Open Source
Platforms
- Linux