PocketSOC
Mobile incident response app that lets SOC teams view detections, isolate hosts, and manage alerts from CrowdStrike, Microsoft Defender, and AWS GuardDuty directly from their phone.
Cost / License
- Subscription
- Proprietary
Platforms
- iPhone
- iPad
- Android
- Online
- Software as a Service (SaaS)
Features
PocketSOC information
What is PocketSOC?
PocketSOC™ keeps on-call SOC analysts connected to critical detections wherever they are.
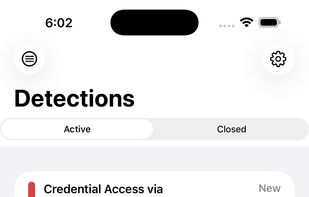
Designed for mobile incident response, PocketSOC integrates with CrowdStrike Falcon APIs, Microsoft Defender, and AWS GuardDuty to deliver a focused, no-noise view of what matters most. Instantly access a streamlined feed of Active and Closed detections with powerful search, filters, and objective targeting.
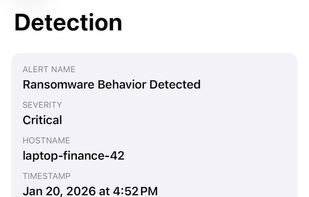
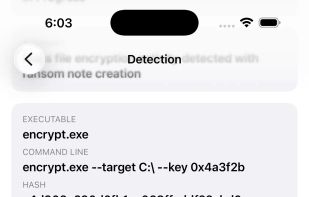
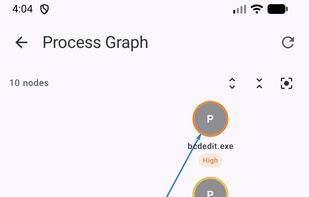
Drill into rich detection details built for fast decision-making: MITRE ATT&CK context, host and user, process command line, hashes, DNS requests, file writes, child process counts, and a one-tap link to open the detection directly in Falcon.
When it’s time to act, PocketSOC keeps control deliberate and secure. Isolate a host or lift isolation only after explicit confirmation and Face ID authentication. Close detections or assign them to a teammate with confidence—no rushing to a laptop required.
Push notifications deep-link you straight into the detection, reducing time to awareness and response.
Security-first by design: credentials and tokens are stored securely in Keychain, no secrets are logged, and containment actions are double-gated to prevent mistakes under pressure.