Flowtriq
Flowtriq runs directly on your servers, detects DDoS attacks in under a second, and automatically deploys BGP FlowSpec rules, RTBH blackholes, and cloud scrubbing to stop them.
Cost / License
- Subscription
- Proprietary
Application type
Platforms
- Software as a Service (SaaS)
- Online
Features
Properties
- Lightweight
Features
- Dark Mode
- Website Monitoring
- Command line interface
- Ad-free
- Network Tools
- DDoS Protection
Flowtriq News & Activities
Recent activities
- POX updated Flowtriq
- flowtriq_altto added Flowtriq
- flowtriq_altto added Flowtriq as alternative to FastNetMon, Cloudflare, Andrisoft WanGuard and NetFlow Analyzer
Flowtriq information
What is Flowtriq?
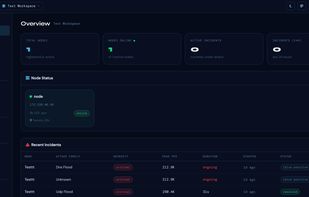
Flowtriq is a real-time DDoS detection and auto-mitigation platform that runs directly on your Linux servers rather than sitting in front of your traffic as a proxy. The core idea is simple: most DDoS protection tools find out about an attack the same way you do, after something breaks. Flowtriq's agent checks traffic every single second, builds a dynamic baseline of what normal looks like for each server, and detects anomalies the moment they appear. From detection to first mitigation action takes under one second.
When an attack is detected, Flowtriq classifies it automatically. It identifies eight attack types including SYN floods, UDP floods, DNS amplification, NTP amplification, ICMP floods, HTTP floods, GRE floods, and multi-vector attacks. It also does payload-level IOC pattern matching against a library of over 65,000 known threat indicators, which means it can identify specific botnets like Mirai variants and LOIC by their packet signatures rather than just by traffic volume.
Mitigation runs through a configurable escalation policy. Flowtriq starts with the most surgical option available: per-server iptables rules, null-routes, or CDN firewall rules depending on what you have configured. If the attack exceeds local capacity, it escalates to BGP FlowSpec, which pushes rate-limiting or drop rules to your upstream routers via BGP, filtering attack traffic at the network edge before it reaches your server. If the attack is large enough to overwhelm BGP, it escalates further to cloud scrubbing through Cloudflare Magic Transit, OVH VAC, or Hetzner. The entire chain fires automatically. No one needs to be awake to respond.
Every incident generates a full PCAP capture that includes the pre-attack ramp-up phase. You can download captures from the dashboard, stream them during an active attack, and analyze them in Wireshark. For teams doing post-incident analysis or security research, this data is genuinely useful rather than just a checkbox. Standard plans retain PCAPs for 7 days. Enterprise plans can retain them for up to 365 days.
Alerts fire within one second of detection across Discord, Slack, PagerDuty, OpsGenie, SMS, email, and custom webhooks. Each alert includes the attack type, severity, peak PPS, peak bandwidth, affected node, and botnet confidence score if an IOC match was found. You can configure per-severity escalation policies so a small UDP flood sends a Slack message while a large DNS amplification attack pages your on-call engineer and triggers cloud scrubbing simultaneously.
For teams managing infrastructure across multiple clients, the multi-workspace architecture handles full isolation between workspaces while giving admins a unified view across all of them. Each workspace has its own nodes, incidents, alert channels, status page, and team members. This is the architecture MSPs, hosting providers, and ISPs use to manage DDoS protection across a client base without data leakage between accounts.